Meraki IPSK with FreeRADIUS
This is a follow up to my Post IPSK on Cisco without ISE but FreeRADIUS. The FreeRADIUS server has already been running in the state since that post, and I will show what has to be done specific to the configuration when working with Cisco Meraki APs.
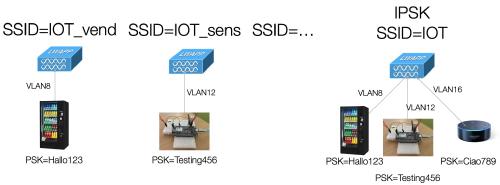
Meraki’s IPSK comes in two flavors: with RADIUS server and without.
The “without” option lets you configure multiple PSKs that are valid to every client that knows them. Numerous vendors support this system, and the AP basically tries all valid PSKs on client join to find the one that matches. The issue with this approach is that it can’t work with WPA3. With WPA3 (and with that, I mean WPA3-SAE, not 802.1X) the AP has to know the correct secret and has no chance of trying multiple possibilities. One vendor claims to have worked around that, but there have yet to be any technical details.
This leaves us with “Identity PSK with RADIUS” - because we “pre-register” our clients with MAC-address in our RADIUS-Server, the AP can query it for the correct passphrase as soon as it receives a join from a client, which makes this possible with WPA3-SAE. But, as of today, Meraki APs (version MR 30.6) do not support this yet. Ciscos 9800 controller supports this starting from 17.9.2, so we can hope that Meraki will support this soon too. The security issue itself is not that big, because some of the weaknesses of WPA2-PSK are a bit offset by IPSK, but missing WPA3 support also means no IPSK in 6 GHz, as WPA3 is required for the 6 GHz band.
Having said the theoretical parts of this post, let’s get to configuring.